One of the most common pitfalls organizations face after a cyberattack is not reporting the incident immediately to CISA, either because they’re waiting for “the perfect time” to report or because they’re unsure about the severity of an incident.
Cyber incident reporting to CISA within 72 hours of an incident, a practice mandated in Congress’ 2022 federal funding package and signed into law by President Joe Biden, is a key post-attack step for organizations after isolating impacted systems and datasets.
“Given the severity of a lot of the cyberattacks we’ve seen over the last several years, acting quickly to inform and communicate and bring others into it is really important,” said CISA Cybersecurity Division Associate Director Michael Duffy in an interview with GovCIO Media & Research. “Some can get stuck in terminology, such as, is this technically an incident and should we dig in a little bit and report tomorrow so we have more to report. Very closely related to that is thinking that just one report is sufficient — the best way we at CISA can gain insights and [provide] tailored support is open that line of communication. CISA is very interested in how things were resolved and what you’ve seen on the other side as we are at the very beginning of the suspected incident itself.”
Another common mistake is resuming normal operations too quickly after an incident. Organizations should take the time to conduct a “full analysis and remediation response” before bringing systems back online, Duffy said. This helps organizations ensure the threat is eradicated, but also prevent similar future breaches.
“We in the federal government have been investing a lot in endpoint detection and response solutions to help us gain that greater asset visibility so we can say, we know what the adversaries are after and are able to further protect by applying what we’ve seen across the board,” Duffy said.
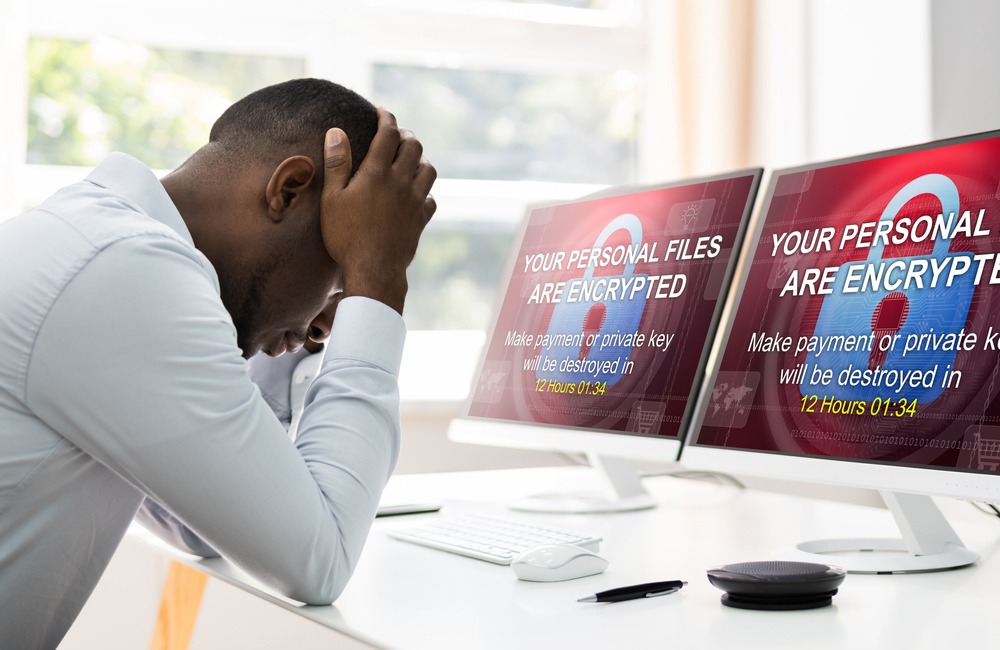
With the 200% rise in ransomware attacks over the past two years and renewed cyber threats from Russian actors relating to the Russian invasion of Ukraine, businesses and federal agencies face increasingly severe cyber threats, from ransomware to phishing attacks.
Isolating and containing a cyberattack, preserving as much data as possible, and communicating with CISA as frequently as possible are critical steps to limiting the scope of the attack and protecting others.
“Things are so connected for ease of use and access so that what may have been a fairly isolated incident in the past is now fairly widespread if not triaged and isolated appropriately,” Duffy said. “Understanding how your system is connected is really important before taking too many steps forward as part of the recovery/response practice.”
The rise of remote work due to the COVID-19 pandemic interconnected networks and IT systems more than ever before, highlighting the importance of a zero trust approach to cybersecurity (also mandated by the White House in its May 2021 executive order).
Zero trust is especially critical given the recent prevalence of identity-related attacks, Duffy said, such as the SolarWinds incident in December 2020.
Despite malicious Russian actors exploiting poorly configured multi-factor authentication (MFA) protocols in a recent incident, Duffy said MFA within a zero trust framework “is one of the most important cyber practices that any organization can implement” because it reduces the risk of compromise by 99%.
“This does not call into question zero trust practices or principles at all, in my opinion, it really does say … this is a good example that one pillar of zero trust isn’t enough, it’s a comprehensive application of zero trust principles [that] is a challenge for organizations,” Duffy said. “The path to zero trust is not simple. Finding those little targets, like configuring MFA properly, making sure you have proper identity infrastructure and looking at ways to segment your network so that even one breach, or if one defense mechanism fails, you’ve segmented enough to isolate and prevent a widespread breach across your enterprise. That really matters when we talk about critical infrastructure and high-value assets.”
CISA offers a wealth of resources on its website for organizations seeking cyber guidance and threat information. CISA’s Shields Up webpage, which Duffy said is the most visited webpage on the site right now, publishes the latest updates regarding cyber incidents and emphasizes good cyber hygiene practices, which Duffy said is the most important thing any organization can do to reduce cyber risk.
While reporting incidents immediately to CISA and communicating updates throughout incident response is highly important, Duffy said CISA doesn’t want to “burden” organizations with a multitude of guidance and requirements or make the question of, what to do after a cyberattack, more confusing.
The No. 1 step to remember in the event of a breach? Tell CISA, and keep communicating with CISA until the incident is resolved. CISA can also help organizations determine if or when to notify supply chain partners, contracting partners, or other federal agencies, such as the FBI.
“We are always worried about the threat of vigilance fatigue,” Duffy said. “We have been, as a government and a nation, when it comes to cybersecurity, on high alert for almost two years. Our reporting protocol is fairly simple and straightforward via the website: fill out a form and send it in. Keep those lines of communication open.”