Zero Trust
Zero trust is a framework built on the principle of “never trust, always verify,” which is critical for agencies handling sensitive information and operating in complex threat environments. It requires verification for every user, device and application attempting to access resources, regardless of location. This approach assumes that breaches are inevitable and focuses on minimizing the “blast radius” of an attack by limiting lateral movement and enforcing granular access control. For government and defense entities, zero-trust architectures enhance security posture by protecting against insider threats and adversarial external attacks. By implementing it, agencies can better safeguard critical data, systems, and infrastructure, ensuring mission continuity and national security.
-

VA CIO Emphasizes Role of Automation, Cybersecurity in Tech Strategy
Kurt DelBene said the agency plans to increase its spending for cybersecurity.
5m read -

Army Ramps Up Cloud Modernization Ahead of Unified Network
The service's upcoming efforts are honing in on advanced data management and analysis to expedite decision-making and joint operations.
5m read -
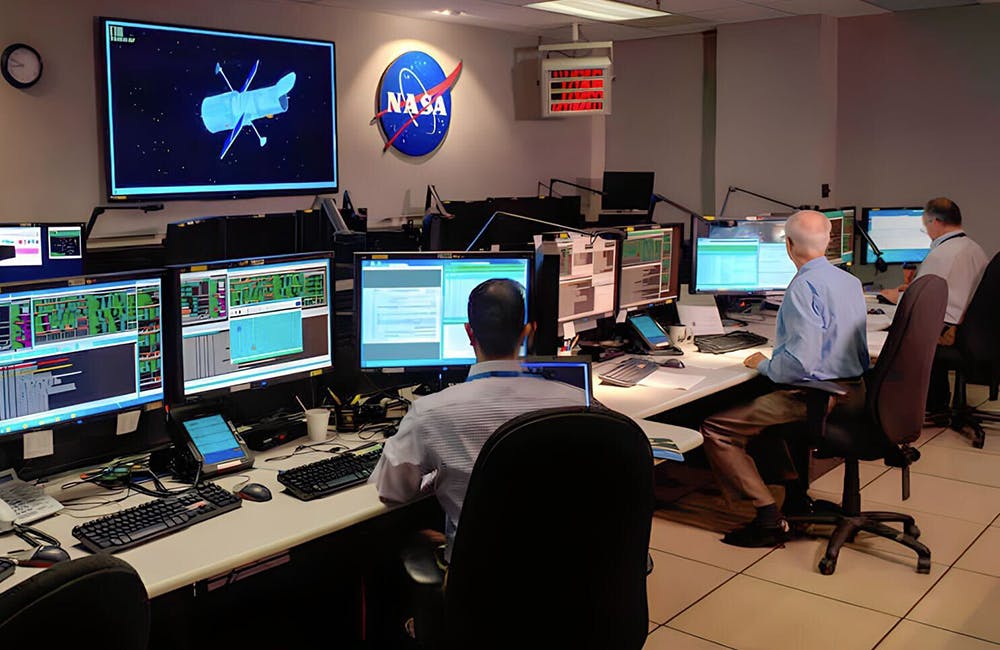
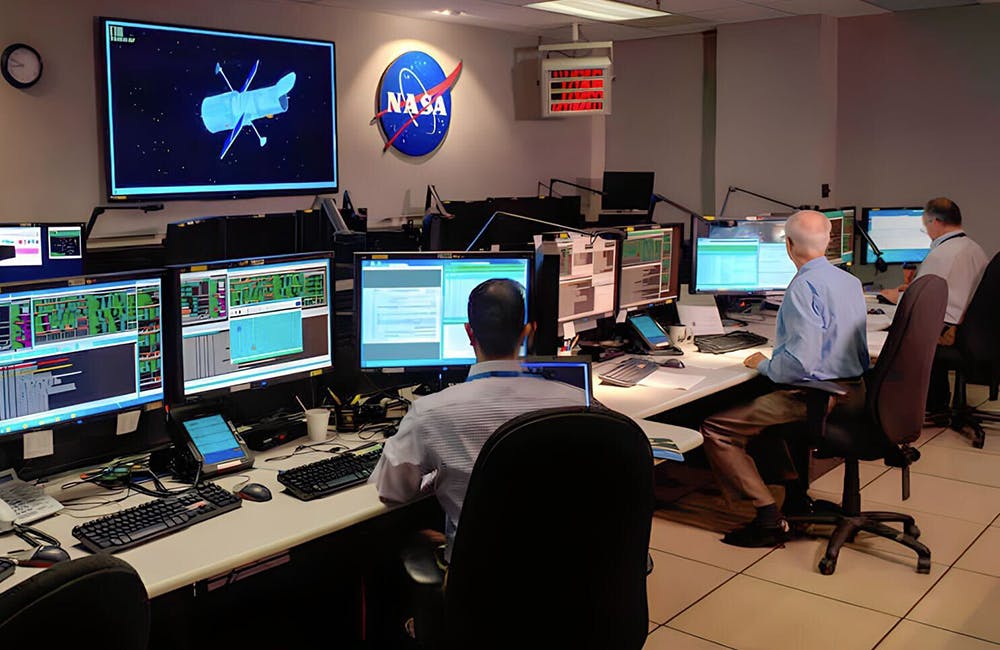
Why a Common Language is Key to Zero Trust
Both NASA and FDIC say government needs to facilitate common language for communication that results in action.
5m read -

Zero Trust Adoption Requires a Culture Shift, Cyber Leaders Say
Leaders are focused on changing mindsets instead of buying specific tools for zero trust.
5m read -

VA Eyes Emerging Technology in Zero Trust Goals
The agency is looking to keep pace with the rate of technical change as a foundation of its enterprise cybersecurity strategy.
5m read -

The Future of Identity Management is Continuous Verification, HHS OIG Says
Automation is a key driver for sustainable identity management and zero trust.
5m read -

DISA Extends Thunderdome Zero Trust Prototype for Classified Network
The six-month extension will allow DISA to develop a SIPRNet-specific zero trust solution for JADC2.
5m read -

CIOs are Implementing Zero Trust to Secure IT Infrastructure
CISA’s Robert Costello and Commerce’s Nagesh Rao talk zero trust, standardization and culture change.
8m read -

Hangar 18 Accelerates Aircraft Repair with Rapid Data Exchange
A software factory named for the legendary UFO repository proves innovation is 'everlong' at the Air Force.
5m read -

Navy to Release Cyber Readiness, DevSecOps Guidelines Ahead of Zero Trust
The service is expected to issue a memorandum regarding policies that will support the cyber ready concept and continue to grow the use of DevSecOps.
5m read -

Zero Trust Could Help Solve JADC2’s Communication Problems
DOD space leaders want rapid, iterative development of JADC2 capabilities, but need to communicate securely.
5m read -

DOD, OMB Agree Identity Management Is Key To Implementing Zero Trust
Identity management, level of assurance and single source of truth are pillars of the zero trust approach to cybersecurity.
5m read